Two practices, one discipline
AI platforms that turn decisions into competitive advantage. Cybersecurity that holds up to real auditors and real adversaries. Pick a side to explore.




Custom AI platforms that turn decisions into competitive advantage — and the cybersecurity that protects the upside. For private equity, financial services, healthcare, technology, and the regulated sectors where both matter.
AI platforms that turn decisions into competitive advantage. Cybersecurity that holds up to real auditors and real adversaries. Pick a side to explore.




Strategic guidance to identify high-impact AI opportunities and build a pragmatic roadmap.
End-to-end design and delivery of custom AI platforms tailored to your business.
Hands-on programs that give your team the skills and confidence to leverage AI effectively.
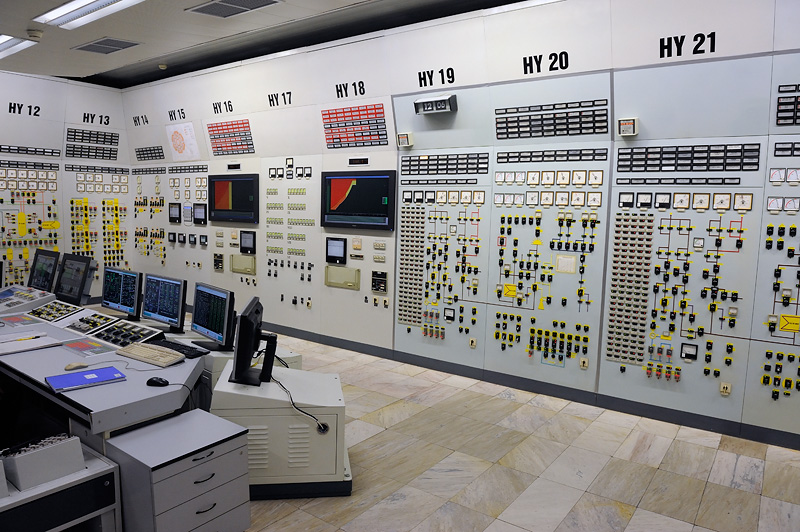
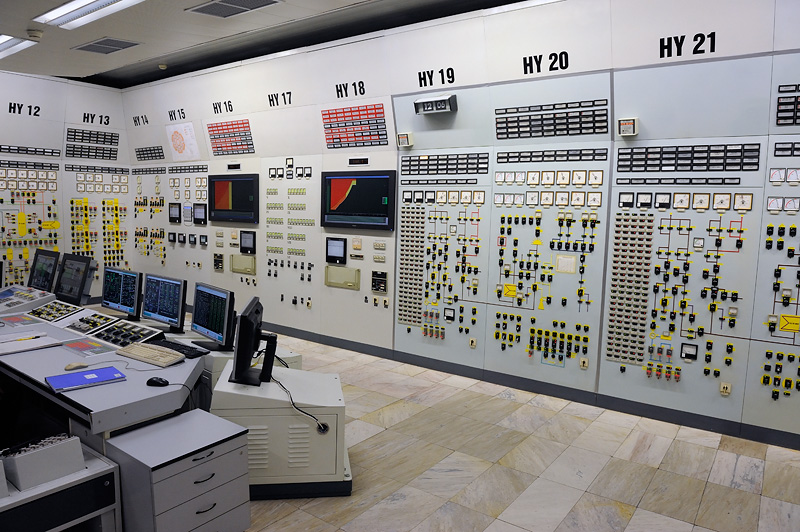
Scoped reconnaissance and gap analysis against the framework that matters to you — NERC CIP, 10 CFR 73.54, NIST CSF, IEC 62443, ISO 27001, SOC 2, HIPAA, or a custom baseline. Findings prioritized by dollar exposure and exploitability — not severity ratings nobody acts on.
Hands-on execution. Security architecture, control implementation, and the program documentation auditors and regulators actually accept. Engineered to hold up under inspection — not paper that fails the first time it's tested.
A program is only as good as the next audit — and the next attack. Retainer-based advisory, periodic reassessments, tabletop exercises, and continuous monitoring. Posture decays without maintenance. We keep yours from drifting.
Intelligence unlocks value. Defense keeps it compounding.
Cambonic builds AI platforms that turn decisions into competitive advantage — compressing weeks of research into days, surfacing insight out of years of operational knowledge, and putting leverage directly in the hands of the people running the business. Intelligence isn't a feature. It's a value-creation lever.
And because the value we engineer is worth protecting, we also defend it. The same team that built the upside understands how to keep it — from regulators, from auditors, and from real adversaries who would rather capture the value than create it.
Not slide decks. Not proof-of-concepts that gather dust. Working systems that compound returns. Defenses that hold.
Whether you have an AI platform in mind, need a security assessment, or just want to explore what's possible — reach out.
hello@cambonic.com